Remain Notified with the Universal Cloud Storage Press Release by LinkDaddy
Wiki Article
Exactly How Global Cloud Storage Solutions Can Improve Data Safety And Security and Compliance
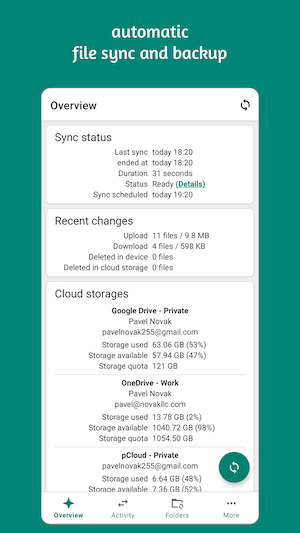
In the world of information protection and compliance, the advancement of global cloud storage space solutions has actually provided a compelling service to attend to journalism issues dealt with by organizations today. With an array of innovative features such as enhanced information encryption, automated conformity tracking, secure information accessibility controls, calamity recuperation options, and regulative compliance automation, the duty of cloud storage services in strengthening data security and adherence to industry policies can not be downplayed. However, the ins and outs of just how these solutions effortlessly incorporate into existing processes and systems to boost safety and security standards and conformity protocols might just use a fresh viewpoint on the intersection of technology and information governance.Boosted Data Encryption
Enhancing information security strengthens the protection procedures of cloud storage solutions, making certain robust defense for delicate details. By carrying out advanced encryption formulas, cloud provider can dramatically lower the risk of unapproved accessibility to saved data. Security works by converting plain message information right into ciphertext, which can just be deciphered with the corresponding decryption key. This process includes an additional layer of security to data, making it extremely hard for cybercriminals to intercept and misuse details.Additionally, enhanced information file encryption plays an important role in governing compliance, particularly in industries with strict data protection requirements such as health care and finance. In verdict, prioritizing boosted information security is important for fortifying the protection posture of cloud storage space services and preserving information discretion.
Automated Compliance Monitoring
The application of boosted information security within cloud storage solutions not just fortifies data security yet also establishes the foundation for automated compliance monitoring mechanisms. Automated conformity surveillance plays a crucial role in making certain that organizations comply with sector policies and inner policies regarding data taking care of and storage. By integrating automated compliance tracking tools into cloud storage space services, organizations can streamline the procedure of tracking and implementing conformity requirements. These tools can instantly scan information stored in the cloud, identify delicate info, and guarantee that it is dealt with according to applicable guidelines. Automated conformity tracking can create real-time records and informs to inform stakeholders of any non-compliance concerns, enabling for timely removal actions. On the whole, the assimilation of automated conformity surveillance within global cloud storage services enhances information safety and security by providing organizations with a positive method to maintaining compliance and mitigating dangers connected with data breaches and governing charges.Secure Data Accessibility Controls
Just how can companies efficiently handle and apply safe information gain access to manages within cloud storage solutions? Protected data access controls are vital for preserving the discretion and honesty of delicate info stored in the cloud.Additionally, organizations can use encryption techniques to protect information both in transit and at remainder within the cloud storage atmosphere. By combining these approaches, companies can improve data security and reduce the dangers linked with unauthorized access in cloud storage services.
Catastrophe Recuperation Solutions
In the world of cloud storage solutions, robust disaster recovery remedies play a crucial function in guarding information honesty and continuity despite unforeseen disruptions. These services are crucial for companies to mitigate the impact of catastrophes such as hardware failings, cyber-attacks, or all-natural catastrophes that could possibly lead to information loss or downtime.
Carrying out a detailed disaster healing strategy involves creating back-ups of crucial data and applications, establishing repetitive systems for failover capabilities, and specifying clear procedures for bring back operations promptly. Cloud storage solutions supply advantages in disaster healing by giving scalable storage space options, automated backups, and geographically varied information facilities that enhance redundancy and strength.

Regulatory Compliance Automation
Amidst the essential realm LinkDaddy Universal Cloud Storage Press Release of disaster recuperation services within cloud storage solutions, the assimilation of regulative conformity automation emerges as a pivotal system for making sure adherence to industry criteria and lawful requirements. Regulatory conformity automation includes using technology to simplify the procedure and streamline of meeting regulative commitments, such as data protection regulations like GDPR or industry-specific criteria like HIPAA in health care. By automating jobs such as data encryption, access controls, and audit routes, organizations can significantly minimize the risk of non-compliance and the associated fines.
Conclusion
With an array of innovative attributes such as improved information security, automated conformity tracking, protected information accessibility controls, disaster recuperation options, and regulative compliance automation, the role of cloud storage services in fortifying information security and adherence to industry laws can not be underrated.The application of boosted data encryption within cloud storage services not only fortifies data protection yet also sets the structure for automated conformity tracking systems. On the whole, the integration of automated conformity tracking within global cloud storage space solutions boosts data security by giving organizations with a positive approach to maintaining compliance and mitigating risks associated with data breaches and regulative charges.
In conclusion, universal cloud storage solutions use improved information security, automated conformity monitoring, protected data accessibility controls, calamity healing remedies, and governing conformity automation. By utilizing these solutions, companies can alleviate risks associated with information breaches, make sure regulative conformity, and boost general information security actions.
Report this wiki page